7 layers of OSI Model And Their Functions
Table of Contents
An open system interconnection (OSI) model is a conceptual model that allows two different systems to communicate using standard protocols even with different architecture. The OSI model partitions a communication system into various layers. Each layer has a set of special standard communication protocols.
OSI Model
OSI stands for Open System Interconnection. An open system is a model that allows any two systems to communicate even if their architectures are different. OSI is a supermodel for communication between different computers. It is a complete model that covers all aspects of network communications.
International Standard Organization (ISO) was designed the OSI model in the late 1970s.
What are the Protocols used in OSI Layers?
Protocols are a group of formatting and rules that allow the standardization of the exchange of data in order. Multiple systems can communicate with one another in a proper way. They also allow different operating systems and applications to speak.
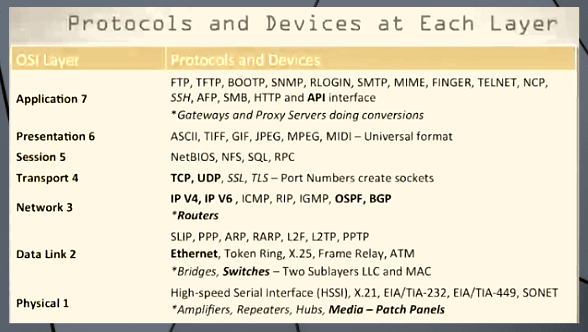
Before we mention standard protocols, Apple computers never interact with Microsoft computers. Different protocols have unique features and goals. And different network models grant permission to different services which will be handled by various protocols at different layers of the OSI model.
TCP and IP transmission control protocol/Internet Protocol are both samples of commonly used protocols. Here are the brief details of major protocols that exist within the different layers of the OSI model.
The original version of the OSI model has seven layers. Each layer tackles a particular job and communicates with layers above and below itself by using a set of standard communication protocols.
The Application Layer is the seven-layer of the OSI model that has APIs or application interfaces that enable applications to speak with other applications in a clear format.
Within the Transport Layer, two common protocols TCP (transmission control protocol) and UDP (User Datagram Protocol) exists.
At the Network Layer, we’ve IP or Internet Protocol version 4 and version 6 OSPF open shortest path first, and BGP border gateway protocol routers operate at the third layer.
The Data Link Layer has the Ethernet protocol and this is often also where switches operate switches are generally layer 2 devices. Although there are some advanced switches that will operate at layer 2 and layer 3 of the OSI model. That switches operate typically at the info link layer or layer 2 layers 1.
The Physical Layer generally contains media like pieces of cabling or Wireless or another sort of communication technology. this is often also where we’ve patch panels where our cabling and our building close in single interface hubs and repeaters also operate at the physical layer or layer 1 of the OSI model.
OSI Model Layers
OSI model consists of seven layers. Each layer in this model performs a specific function in network communication.
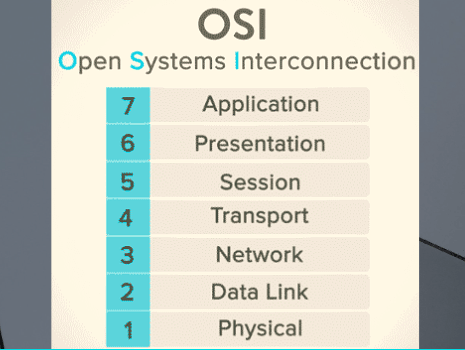
OSI model is also called Reference Model because it presents an idea rather than reality. No communication protocol follows this model by 100%.
- Application Layer
- Presentation Layer
- Session Layer
- Transport Layer
- Network Layer
- Data Link Layer
- Physical Layer
7. Physical Layer
The physical layer is the primary layer of the OSI model. It sends out a stream of bits and describes how the data is transmitted over the network and also what kind of control signals are used. Its main function is to control how a stream of bits is sent and received over the physical medium.
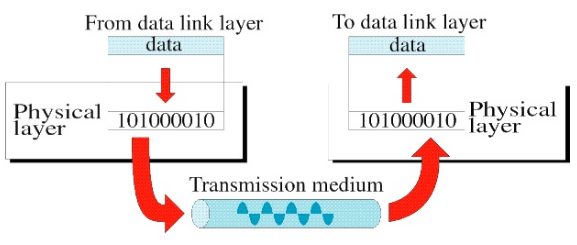
Furthermore, the physical layer must decide the following:
- Characteristics of Media: the physical layer defines the nature, qualities, and type of transmission means.
- Representation of Bits: the bits are encoded into electrical signals for transmission. The physical layer also defines the type of encoding.
- Data Rate: The physical layer defines the number of bits that will be sent in each second.
- Synchronization: the clocks of the sender and receiver are also synchronized.
- Line Configuration: the physical layer defines the attachment of communication devices with the medium.
- Transmission Mode: the physical layer identifies the track of transmission between two devices simplex, half-duplex or full-duplex.
Common protocols used at this level are IEEE 802, IEEE 802.2, and FDDI.
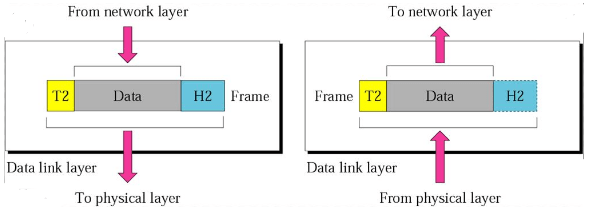
6. Data Link Layer: Layers of the OSI Model
Data Link Layer is responsible for the reliability of the established physical link. It is further divided into two sub-layers LLC and MAC. LLC ensures the reliability of the physical connection. MAC specifies how workstations cooperatively share the transmission medium.
-
LLC
LLC stands for Logical Link Control. It is also the upper sub-layer. It ensures the reliability of the physical connection. The standard protocol IEEE 802.2 is the most commonly used standard.
Point-to-Point Protocol (PPP) is also an important standard at this OSI level. It is used to communicate across point-point links. It is an important protocol for wide-area networking.
-
MAC
MAC stands for Media Access Control. It specifies how workstations cooperatively share the transmission medium. The IEEE 802.3 standard specifies a medium-access method known as “Carrier Sense Multiple Access With Collision Detection (CSMA/CD).”
The Data link layer must decide the following:
- Framing: the data link layer break down the stream of bits into maintainable data units known as frames.
- Flow Control: if the rate of sending data is more than the rate of receiving data, the data link layer imposes a flow control mechanism to prevent this situation.
- Error Control: the data link layer distinguishes and retransmits damaged or misplaced frames. It also averts the duplication of frames.
- Access Control: if two or more devices are connected to a similar link, the data link layer determines which device has control over the link at a given time.
5. Network Layer
The network layer functions for building, maintaining, and terminating network connections. It also manages the delivery of data from source to destination. Furthermore, the Network layer determines a logical path between the sender and the receiver over a computer network.
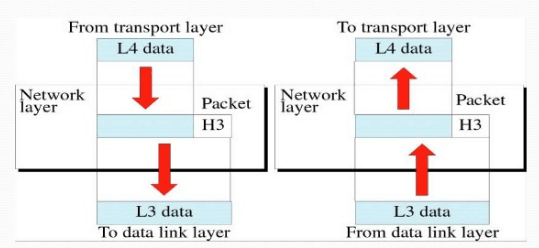
There may be many networks between two computers. This layer manages to send data from the source computer to the destination computer. The most commonly used protocols that operate at this stage are IP, IPX, and X.25.
4. Transport Layer: Layers of the OSI Model
The transport layer controls the flow of data as well as ensures that messages are delivered error-free. It also divides huge messages into small packets for proficient transmission. These packets are reassembled, checked for faults and acknowledged at the receiving side.
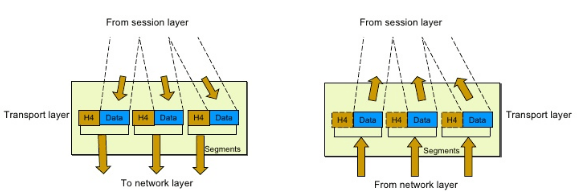
The data is retransmitted if error arises during transmission. Common protocols that operate at the transport layer are TCP, UDP, SPX, and NetBEUI.
3. Session Layer
The session layer set up, control, and terminates user connections. A session is a swap of messages among computers. It also synchronizes user tasks. Synchronization includes the use of checkpoints in a data stream. If a breakdown occurs, only the data from the last checkpoint is retransmitted.
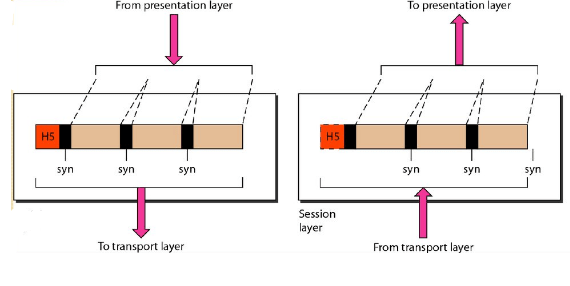
Assume we desire to send 1000 pages of data. Checkpoint can be used after every 100 pages. If there is a fault on page 320, the pages from 301 will be retransmitted. Page from 1 to 300 will not be retransmitted. Winsock and NetBIOS are usually shown as functioning at the session layer.
2. Presentation Layer: Layers of the OSI Model
The presentation layer does data reformatting, compression, and data encryption. It changes data according to both the sender format and the receiver’s format. The presentation layer compresses a large amount of data into small sizes as well as encrypts that data earlier than the transmission.
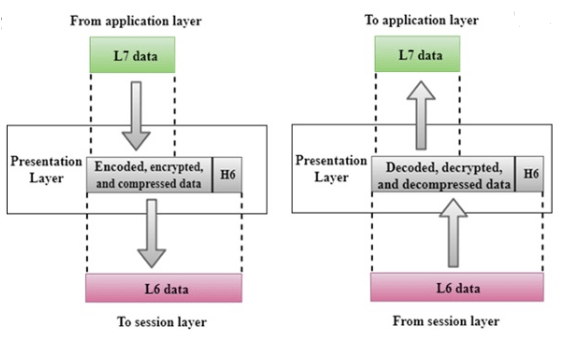
The presentation layer performs the following functions in the OSI Model.
- Data Reformatting: when two computers swap data, the data is changed to bitstreams before it is transmitted. Two computers may use different encoding techniques. The presentation layer at sending computer changes data according to the sender format and the presentation layer at receiving computer changes data according to the receiver’s format.
- Encryption: the presentation layer encrypts the data earlier than transmission. It means that the sender transforms the unique information into another form and sends the resulting message over the network. The receiver again transforms the message back to its original form. It is called decryption.
- Compression: data compression reduces the number of bits to be transmitted. The presentation layer compresses a large amount of data into small sizes.
Common protocols that operate at the presentation layer include SMB, NCP, and NFS also.
1. Application Layer
The application layer is the uppermost layer of the OSI model. It provides services directly to user applications and allows the user to access the network. It also provides user interfaces and support for services such as email, remote file access database management, and other distributed information services.
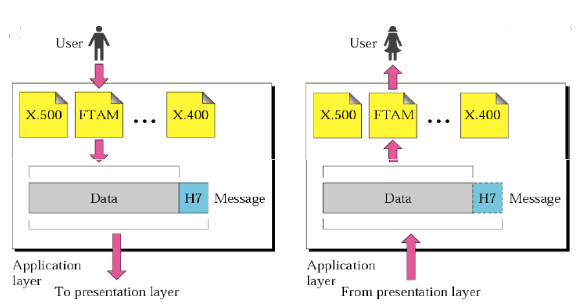
- File Transfer: it allows a user to access, retrieve and manage files on a remote computer
- Mail Services: it provides the basis for email forwarding and storage facilities.
- Directory Services: it provides distributed database sources and access for global information about various objects and services also.
Read About:
- Types of Operating System
- Steps In Booting Process
- Fyptt APK Latest Version 5.0
- Watch Online Movie Apk
- Types of Network Protocols