Types of Communication Protocol In Telecommunication
Table of Contents
In telecommunication, a communication protocol is the set of rules that allows two or more entities of a communication system to transmit information via a kind of variation of a physical quantity. These are the rules and standards that define-syntax.
Semantic synchronization communication in possible layer recovery methods. This article is all about the importance of communication protocols, functions of communication protocols with their important types.
Read Also:
- Types of Scheduling Algorithm in OS
- Types of CPU Scheduling
- Types CPU Threads
- Multithreading And Its Models
Types of Communication Protocol
Important types of communication protocol are as follows:
- TCP/ IP
- UDP
- DHCP
- SMTP
- SNMP
- FTP
- SFTP
- TFTP
- POP3
- IMAP4
- HTTP
- HTTPS
- NAT and ICS.
TCP/ IP
TCP stands for transmission control protocol. It provides full transport layer services to applications, it is a reliable stream transport port-to-port protocol. The term stream means connection-oriented.
It means that the sender cannot send a message until the receiver is contacted and agrees to a communication. TCP generates a virtual circuit between the sender and receiver by creating this connection. The connection remains active for the duration of a transmission.
In this way, the receiver knows to expect the entire transmission rather than a single packet. TCP communication protocol is a connection-oriented service. It is responsible for the reliable delivery of the entire stream of bits contained in the message generated by the sending application.
Reliability is ensured by providing error detection and retransmission of damaged frames. All segments must be received and acknowledged before the transmission is considered complete and the virtual circuit is discarded.
At the sending end, TCP divides long transmission into smaller data units and packages each into a frame called a segment. Each segment includes a sequencing number for reordering after receipt and an acknowledgment id number.
TCP/ IP Communication Protocol Features
Some important features of TCP are as follows:
- Connection Opening
- Flow Control
- Sequencing
- Acknowledgment
- Error Detection
- Connection Closing
Connection Opening
On the sending host, a process such as a web browser issues a request to send data to a destination host such as a web server. TCP creates an initial segment designed to open the connection between the sender and receiver.
In this initial contact, the two systems exchange IP addresses and port numbers and set up the flow control and sequencing.
Flow Control
The sending and receiving hosts exchange the number of bytes to be accepted at on time. In this way, the sender sends an amount of data that can be handled by the receiver. The amount of data can be changed as the circumstances change on each machine.
Sequencing
Every segment is assigned a sequence number. The sequence number is stored in the first byte in every segment. This technique is used by the receiving host to reassemble any segment that arrives out of order.
Acknowledgment
When TCP transmits a segment, it holds the segments in a queue until the receiving TCP issues an acknowledgment that the segment has been received. The sender retransmits the segment if it does not receive the acknowledgment.
Error Detection
A value in the header is used by the receiver to test the integrity of the incoming segment. The receiver sends an error message to the sender if the segment is corrupted. The sender then immediately retransmits the segment.
Connection Closing
The connection is closed when no more data is to be sent. The sending TCP sends a segment that tells the receiver that the socket should be closed.
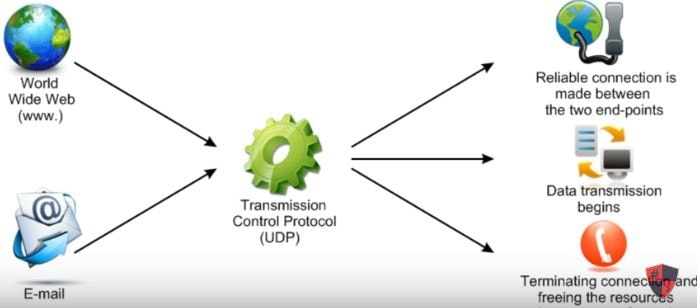
UDP
UDP stands for user datagram protocol. It is a connectionless service. It means that the sender does not have to first establish a link to the receiver before transmitting data. UDP communication protocol is a simple transport protocol.
UDP is a very important type of communication protocol. It adds only port addresses, error control, and length information to the data from the upper layer. The packet produced by UDP is called a user datagram.
A brief description of its fields is as follows:
Source Port Address: it is the address of an application program that creates a message.
Destination Port Address: it is the address of an application program that receives the message.
Total Length: it defines the total length of the user datagram in bytes.
Checksum: it is a 16-bit field that is used in error detection.
UDP provides only basic functions required for end-to-end delivery of transmission. It does not provide any sequencing or reordering functions. It cannot specify the damaged packet when an error occurs. UDP does not contain an ID or sequencing number for a particular datagram.
DHCP
Dynamic Host Configuration Protocol (DHCP) is the most frequently used method of the dynamic IP address. The servers that manage the dynamic assignment of IP addresses are called DHCP servers. The workstations that are dynamically assigned IP addresses by DHCP servers are called DHCP clients.
DHCP software resides on clients and servers to manage the dynamic assignment of IP addresses.
The range of IP addresses to be assigned to the client is specified when DHCP servers are configured. DHCP servers maintain a list of currently assigned IP addresses from the assignable IP address range. A client can be assigned any IP address from an assignable list.
How DHCP Communication Protocol assigns an IP address?
DHCP servers can assign an IP address in three different ways:
Automatic Allocation: in automatic allocation, the server attempts to always assign the same address to a given host or ode. It is useful for the hosts that provide services to users such as mail servers. Such type of host needs the same address each time because other hosts may have saved their internet address.
Dynamic Allocation: in dynamic allocation, an IP address is automatically assigned to a client in a TCP/IP network. It is typically assigned by a DHCP server each time the client logs on to the network.
Manual Allocation: in manual allocation, a network administrator assigns an address to a particular host or node.
The DHCP process starts when the client sends a broadcast message to locate the DHCP server. The broadcast message contains the client’s ID, request for IP address, and desired options such as subnet mask, DNS server, domain name, and a static route.
The broadcast message that is sent is called a DHCPDISCOVER message. Each DHCP server that receives this message can send the DHCPOFFER message to the client to offer an IP address that is not currently in use. Typically, the least recently used address in the server’s assignable address list is selected.
The client indicates its acceptance of the IP address by broadcasting the DHCPREQUEST message. The server acknowledges the client’s acceptance of the IP address in the DHCPACK message. The message also delivers additional configuration information to the client.
SMTP Communication Protocol
SMTP stands for simple mail transfer protocol. It is one of the most popular network services in electronic mail. SMTP communication protocol supports electronic mail on the internet. it is a system for sending messages to other computer users based on email addresses.
SMTP provides the facilities for mail exchange between users on the same or different computers. It also supports:
- Sending a single message to one or more recipients
- To send messages that include text, voice, video or graphics
- Sending a message to users on networks outside the internet.
SNMP Communication Protocol
SNMP stands for a simple network management protocol. It is a management protocol that enables network devices to communicate information about their state to a central system. It also enables the central system to pass configuration parameters to the devices.
In an SNMP configuration, a system acts as the central communication point for all SNMP enabled devices on the network. This system is known as a manager. A software called SNMP agent is set up and configured with the IP address of the manager on each device to be managed and monitored via SNMP.
The SNMP manager can communicate and retrieve information from the devices running SNMP agent software depending on the configuration. The agent can also communicate the occurrence of certain events to the SNMP manager as they happen. These messages are known as traps.
An important part of the SNMP communication protocol is an SNMP management system. It is a computer that runs a special type of software called a Network Management System(NMS). Most NMS applications use graphical maps of the network to locate a device and then it.
File Transfer Protocol (FTP)
The file transfer protocol is an application layer protocol. It provides a method for uploading and downloading files from a remote system running FTP server software. FTP communication protocol uses the TCP transport protocol to guarantee the delivery of data packets.
FTP provides some basic security capabilities such as user authentication. The FTP server can be configured to accept anonymous logins instead of creating user accounts for every user. In this case, the username is anonymous and the password is normally the user’s email address.
Most FTP servers that provide files to the general public operate in this way. FTP is popular for distributing files over the internet. It can also be used within an organization to exchange large files frequently with other people or organizations.
Secure File Transfer Protocol (SFTP)
A problem associated with FTP is that it transmits data between the sender and receiver in an unencrypted format. It is solved in another protocol called secure file transfer protocol. SFTP is based on Secure Shell (SSH) technology.
SSH provides authentication between the sender and receiver in addition to encryption capabilities. SFTP id implemented through client and server software that is available for all commonly used computing platforms.
Trivial File Transfer Protocol (TFTP)
Trivial file transfer protocol is a variation of FTP. FTP and TFTP are both application layer protocols. However, the TFTP communication protocol does not have the security capability or level of functionality like FTP. It uses only UDP as a transport protocol and makes it a connectionless protocol.
It has a lower overhead than FTP. TFTP does not provide directory navigation. FTP provides the commands to navigate around and manage the file system. However, TFTP does not provide such a capability.
POP3 and IMAP4 Communication Protocol
POP3 stands for Post Office Protocol Version 3 and IMAP4 stands for Internet Message Access Protocol Version 4. Both POP3 and IMAP4 are used to download emails from a mail server. The email is transported around the network via SMTP and stored on a server.
It is then downloaded from the server using POP3 and IMAP4. A problem with POP3 is that the password for accessing the mailbox is transferred across the network is clear text. It can be accessed by someone easily. IMAP uses a more sophisticated authentication system that makes it difficult to access the password.
Hypertext Transfer Protocol (HTTP)
Hypertext transfer protocol is used to download text, graphics, multimedia, and other material a Web server. It defines which actions can be requested by clients and how servers should answer these requests. HTTP uses TCP as a transport protocol that makes it a connection-oriented protocol.
It can also use UDP for certain functions. HTTP communication protocol uses a uniform resource locator (URL)to determine which page should be downloaded from the server. The URL contains the type of request, the name of the server being contacted, and the page being requested.
HTTP works at the application layer of the OSI model.
Hypertext Transfer Protocol Secure (HTTPS)
HTTP requests are normally sent in cleartext. It is a critical security problem for some internet transactions such as online banking or e-commerce. The HTTPS protocol is a solution for such an application. It uses a security technology known as Secure Sockets Layer (SSL).
This technology encrypts the information sent between the client and the host. HTTPS uses a TCP transport protocol and operates at the application layer of the OSI model. The URL displays HTTP:// in the address bar instead of HTTPs:// when using the HTTPS protocol. An example of an HTTPS URL address is https://sciencerack.com.